x
m
i
d
a
s
SmartToken
Overview
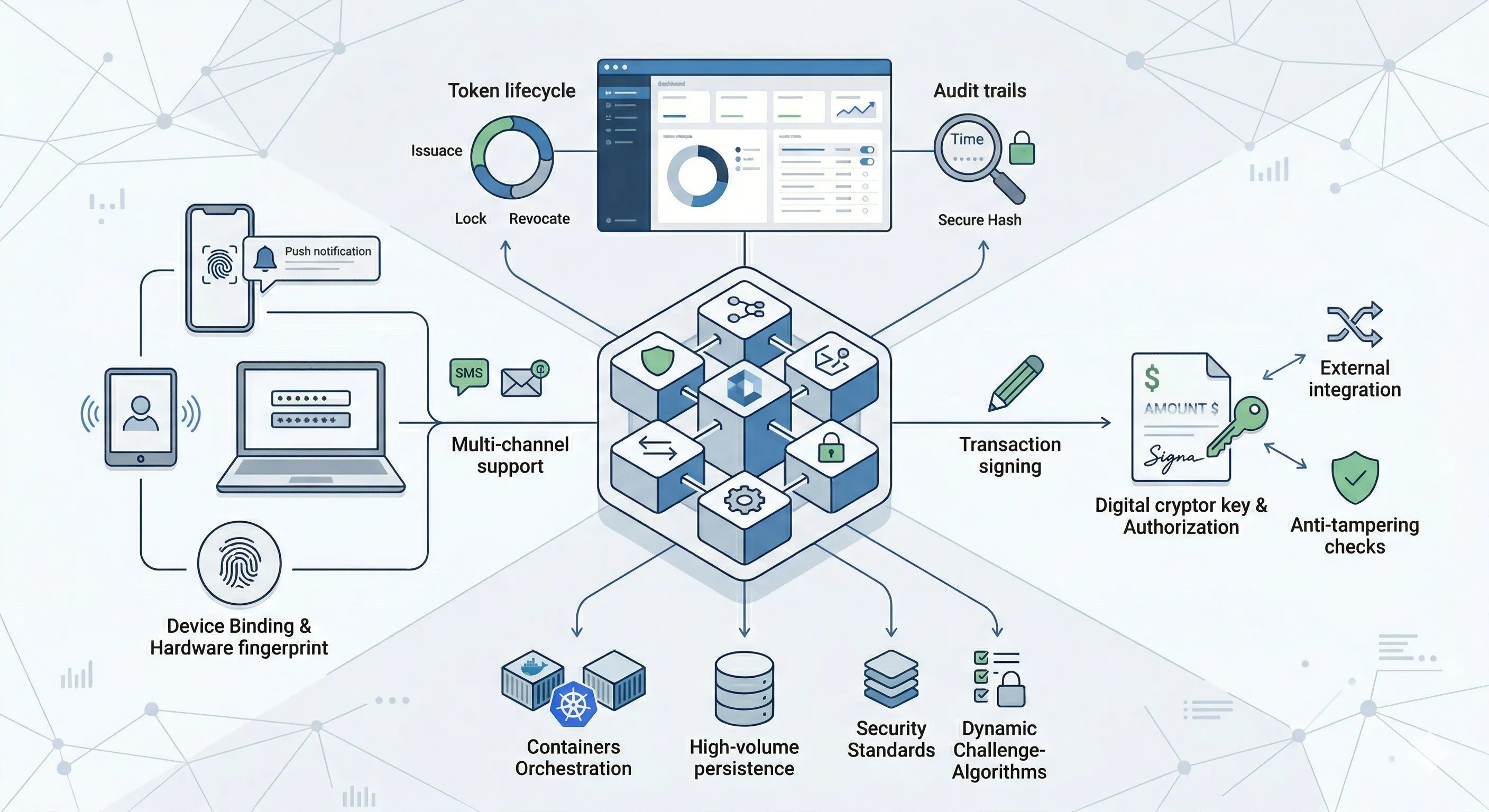
SmartToken: Enterprise-Grade Digital Authentication & Authorization.
SmartToken is a high-performance, Java-based microservices platform designed to replace costly and complex hardware tokens. It provides a secure, scalable, and frictionless way to authorize transactions and authenticate users across web and mobile channels.
Features
Multi-Channel Token Support
Mobile Token
In-app token generation for offline or online transaction authroziation and user authentication.
Device Binding
A "Trust No One" approach that binds the digital identity to a specific device’s hardware fingerprint (IMEI/UUID), preventing credential cloning.
Biometric Tokenization
Integration with FIDO2/WebAuthn, allowing users to sign transactions using FaceID, TouchID, or Android Biometrics.
Web App Tokens
- With Challenges: Synchronous flows where the server sends a challenge the user must solve.
- Without Challenges: Seamless background synchronization for low-risk actions.
SMS & Email Fallback
Integrated SMS gateway support for legacy user bases or emergency recovery.
The Authenticator App (Mobile SDK)
A dedicated mobile application (similar to Microsoft or Google Authenticator) that provides:
Push Notifications
Instant "Approve/Reject" prompts for real-time transaction signing.
Offline Mode
Generate 6-8 digit codes even without internet connectivity.
Multi-Account Support
Manage multiple identities or banking profiles within a single app.
Security
Transaction Signing & Authorization
Third-Party Integration
Securely authorize payments or data sharing with external partners using scoped transaction tokens.
Data-Linked Tokens
The token generated is cryptographically linked to the specific transaction data (amount, payee, date).
WYSIWYS Compliance
"What You See Is What You Sign." The user confirms transaction details on-screen, which are then hashed into the OCRA signature.
Anti-Tampering
Any modification to the transaction data after the token is generated will result in an immediate signature mismatch at the server level.
MITM Protection
Prevents "Man-in-the-Middle" tampering by ensuring the signature is only valid for that specific intent.
Managment
Back-Office & Management Suite
The administrative portal provides complete control over the token ecosystem
Complete Token Lifecycle Management
- Issuance: Automated or manual onboarding of users.
- Lock/Unlock: Immediate suspension of tokens in case of reported theft or suspicious activity.
- Revocation: Permanent decommissioning of tokens for offboarded users.
Audit & Forensics
- Complete Traceability: Every "Approve," "Reject," or "Timeout" is logged with a secure hash.
- Fraud Investigation: Advanced search filters to track IP addresses, device IDs, and geolocations used during authentication.
Advantages
Technical Advantages
Built for the modern enterprise, SmartToken leverages a cloud-native stack to ensure high availability and seamless integration.

Core Engine
Developed in Java for high-performance service execution.
Architecture
Microservices-based, allowing independent scaling of the Authentication, Token Lifecycle, and Audit modules.
Containerization
Fully compatible with Docker and Kubernetes/OpenShift for automated scaling and orchestration.
Database & Persistence
Supports high-volume RDBMS (Oracle, PostgreSQL) with optimized indexing for rapid audit retrieval.
Security Standards
- Algorithms: Supports SHA-256, SHA-512, HMAC, RSA, AES and other encryption supported by Java Cryptography.
- Protocols: Fully compliant with OATH standards (TOTP - Time-based One-Time Password and HOTP - HMAC-based One-Time Password, OCRA - OATH Challenge-Response Algorithm).
- API Security: All endpoints are secured via mTLS and OAuth2/OpenID Connect.
Dynamic Challenge-Response
Move beyond static codes. Generate signatures based on server-side challenges and user-inputted data.
Mutual Authentication
Supports client-to-server and server-to-client verification, eliminating the risk of rogue servers or phishing sites.
Technical Specifications
Platform Performance & Technical Specifications
| Attribute | Specification |
|---|---|
| Performance | Capable of processing 5,000+ authentications per second (TPS) with sub-~100ms latency. |
| Scalability | Horizontal auto-scaling via Kubernetes to handle peak season transaction loads. |
| Reliability | Active-Active deployment support across multiple data centers for 99.99% availability. |
| Interoperability | RESTful APIs and SDKs for Android, iOS, and Web (JavaScript/TypeScript). |
| Security | Hardened against brute-force, replay attacks, and reverse engineering. |
Business Value
Cost Reduction
Zero logistics/shipping costs and no physical battery expiration issues compared to hardware tokens.
Enhanced UX
No need for users to carry an extra device; their smartphone becomes their security key.
Compliance
Meets stringent global banking regulations (PSD2, FFIEC, etc.) for Strong Customer Authentication (SCA).
Reach Us
Modern banking security is complex. Your transition to it shouldn't be.
Ready to eliminate friction and elevate security? Our senior consultants are available for a technical discovery session to discuss your specific throughput, security, and architect a solution tailored to your ecosystem.
Discover More
Explore Our Other Solutions
Midas offers a comprehensive suite of financial technology solutions designed to drive digital transformation and operational excellence.
